Cyber Resilience for every fabricator

In his latest column, Greg Du-feu, Managing Director of Dufeu IT, explains how fabricators can test their Cyber Resilience without spending a fortune.
You don’t need to be a multinational to take cybersecurity seriously — and you don’t need a huge budget to test how strong your defences are.
Every glazing fabricator can assess and improve their cyber resilience using simple, affordable methods that expose weaknesses before criminals do.
Here’s how to test your defences and identify the gaps in your setup — without breaking the bank.
Step 1: Start with a Cybersecurity Risk Assessment
Think of it as a health check for your IT. A professional assessment reviews:
- Device patching and antivirus status
- Network security (firewalls, routers, ports)
- Microsoft 365 and email settings
- Backup and disaster recovery readiness
This highlights critical issues that could lead to downtime or data loss.
Step 2: Run a Phishing Simulation
Staff are the number one entry point for attackers. A simple phishing simulation shows how many people would click a fake link or enter credentials.
Use the results to shape awareness training. It’s one of the most cost-effective improvements any business can make.
Step 3: Check Passwords and MFA
You can test the strength of user passwords and ensure MFA is active across critical systems. Use tools like Microsoft Secure Score or your IT provider’s reporting platform.
If MFA isn’t enabled, you’re running unnecessary risk.
Step 4: Review Your Backup Process
Perform a test restore. Don’t just assume it works.
- Can you restore data from last night’s backup?
- How long does it take?
- Are off-site copies protected from ransomware?
Step 5: Simulate an Incident
Gather your management team and run a tabletop exercise. Pick a scenario — ransomware, email breach, or supplier fraud — and talk through how you’d respond.
Questions to ask:
- Who would make key decisions?
- How would you communicate with staff and customers?
- Do you have a contact list for emergency support?
This builds confidence and highlights missing processes.
Step 6: Review Microsoft 365 Security Settings
Most businesses use Microsoft 365, but very few have hardened the environment. Ensure:
- MFA is enabled for all users.
- Conditional Access restricts risky logins.
- Old accounts are disabled.
- Audit logs are switched on.
These settings cost nothing to implement and drastically reduce breach risk.
Step 7: Use a Vulnerability Scan
Automated tools can scan your network for open ports, outdated software, and known weaknesses. These scans are affordable and give clear, actionable results.
Step 8: Document and Prioritise Fixes
Testing only helps if you act on it.
List every weakness found, rank by severity, and assign ownership for remediation.
Step 9: Retest Regularly
Cybersecurity isn’t one-and-done. Repeat these tests quarterly or after any major IT change.
Step 10: Bring in an External Expert
Even with internal checks, a fresh set of eyes often finds what you’ve missed. A professional penetration test or security review once a year gives real-world assurance.
Why It’s Worth It
Testing your resilience doesn’t just reduce risk — it saves money long-term. You’ll catch problems before they become breaches and show your clients that you take security seriously.
Final Word
You don’t need enterprise budgets to build enterprise-level protection. You just need a structured, proactive approach.
Follow Dufeu IT on LinkedIn, connect with me personally, or visit dufeu-it.co.uk/contact to see how we help fabricators of all sizes test, strengthen, and future-proof their defences.
Latest posts
-
 22/04/2026
22/04/2026Star in the Sty: Elton Boocock
-
 22/04/2026
22/04/2026Keystone Market Research joins Glazpartners initiative
-
 22/04/2026
22/04/2026PiGs Belfast 2026 has arrived!
-
 22/04/2026
22/04/2026Forel signs two-year deal as Premium PiGs Sponsor
-
 22/04/2026
22/04/2026Marrose Abrasives welcomes John Day back after nine years away
-
 22/04/2026
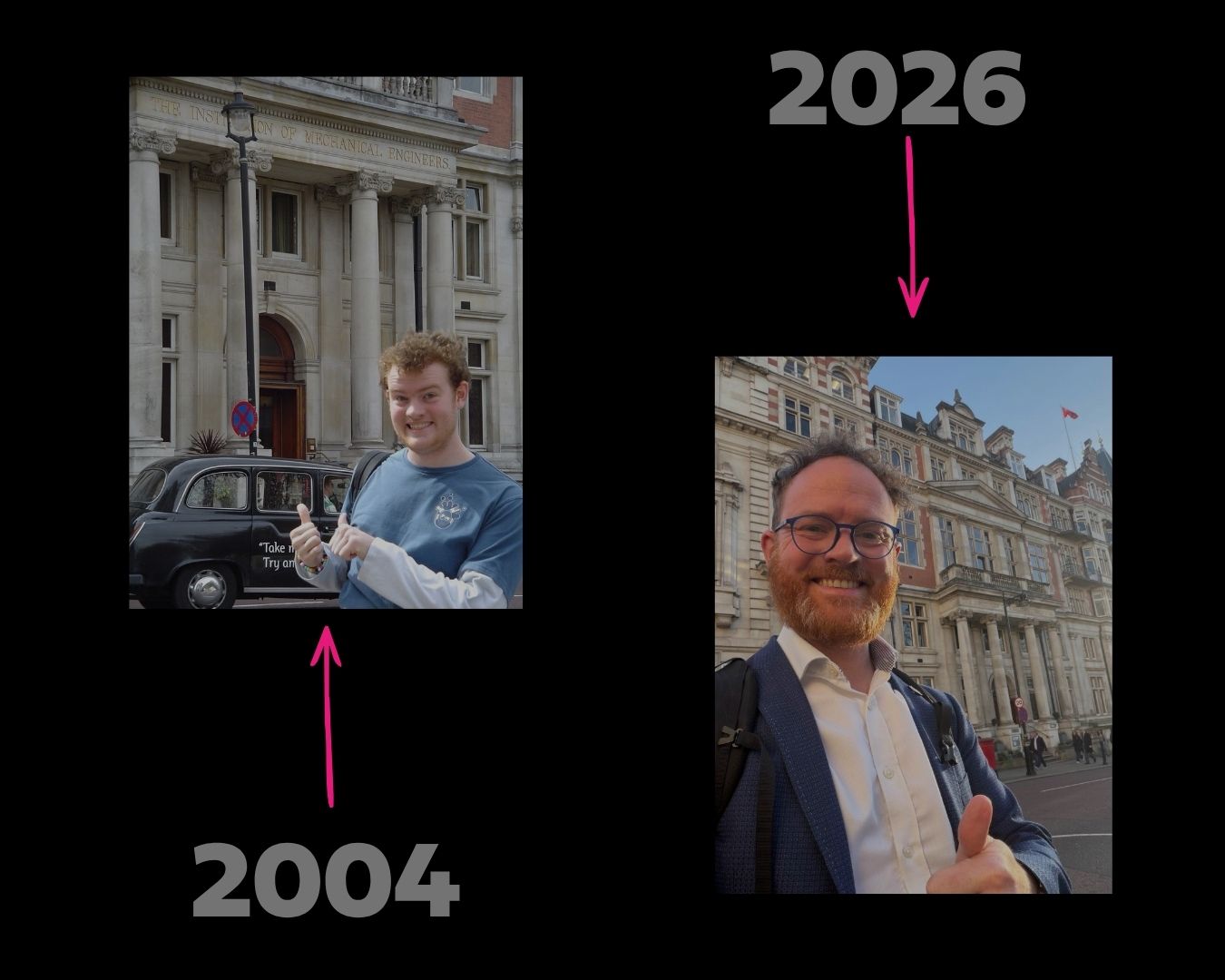
22/04/2026Iain Gray: From student to Director
-
 22/04/2026
22/04/2026Silent View Windows lands Best Heritage Installation award
-
 22/04/2026
22/04/2026Keylite's ModuLite win Best Building Fabric Product award
-
 22/04/2026
22/04/2026Fentrade makes significant machinery investment
-
 21/04/2026
21/04/2026FUHR UK renews Secured by Design membership







